In most world class companies there is an increasing pressure to protect computer networks against unauthorized intrusion, engineering systems are the major concerns of administrators. Their aspiration is to create a robust system that can withstand attack. However, no man made system can be made impenetrable. Our Data Analysis for Network Cyber-Security solutions focuses on monitoring and analyzing network traffic data, with the intention of preventing, or quickly identifying, malicious activity.
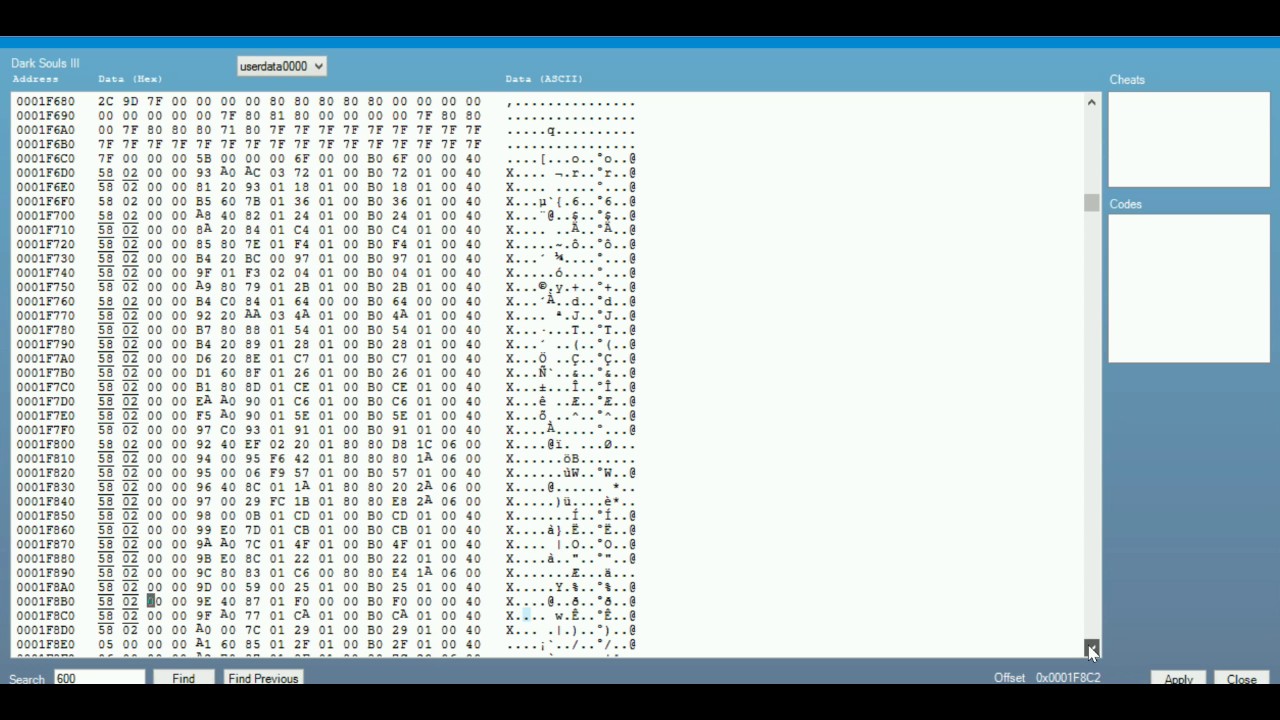
Save Wizard Bypass
Such work involves the intersection of statistics, data mining and computer science. Fundamentally, network traffic is relational, embodying a link between devices. As such, graph analysis approaches are a natural candidate. However, such methods do not scale well to the demands of real problems, and the critical aspect of the timing of communications events is not accounted for in these approaches.
This book gathers papers from leading researchers to provide both background to the problems and a description of cutting-edge methodology. The contributors are from diverse institutions and areas of expertise and were brought together at a workshop held at the University of Bristol in March 2013 to address the issues of network cyber security. The workshop was supported by the Heilbronn Institute for Mathematical Research.
The Real Mc Coy RMC5 Wizard Wah features fuzz-friendly technology, true-bypass, and an under-the-rocker toggle switch to change sweep speed and low end resonance. Effect Type: Wah-WahTechnology: AnalogSpecial Features: True bypassMono / Stereo: Mono In, Mono OutInductor custom manufacture Karmafl. Jan 02, 2021 Now a days Save Wizard kuyhaa supports more then 1000 PS4 games and it’s depends in the game industry is increasing day by day. Because before this amazing software introduced gamer suffer from many worst conditions because they can’t apply cheats to bypass any difficulty in the game play but after its release it becomes the most demanding. Click the button on the toolbar, labeled Not spam. Then select Move to. Open the email from The Save Wizard Team. Click the drop down arrow next to “Reply” in the upper right side the email from header. Click the “Add The Save Wizard Team to Contacts List” from the list that appears.
- The Real Mc Coy RMC5 Wizard Wah features fuzz-friendly technology, true-bypass, and an under-the-rocker toggle switch to change sweep speed and low end resonance. Effect Type: Wah-WahTechnology: AnalogSpecial Features: True bypassMono / Stereo: Mono In, Mono OutInductor custom manufacture Karmafl.
- Now a days Save Wizard kuyhaa supports more then 1000 PS4 games and it’s depends in the game industry is increasing day by day. Because before this amazing software introduced gamer suffer from many worst conditions because they can’t apply cheats to bypass any difficulty in the game play but after its release it becomes the most demanding.
Security and operations teams are inundated with change requests – many of which are still handled manually. In the rush to meet Service Level Agreements, engineers are sometimes forced to compromise security or compliance.
With Desiderata, network engineers can say goodbye to compromising security in the name of expediency. Change management solutions give organizations the awareness and tools they need to securely open and revise access.
Real-time security analysis – Gauge the efficacy of your existing firewall policies, including comparative scoring, to understand current access enforcement.
Policy search – Quickly search all devices within the enterprise domain from a single place in the application
Traffic flow analysis – Trace the source and destination of every rule in each of your existing firewall policies (including NAT) to understand traffic flow.
What We Do
We offer a variety of services to our clients including
Training
Data Center Engineering and Management
Network and System Engineering
Website and Security Analytics
Using expert tools to focus network security and risk analysis enables you to:
- Measure overall network risk posture.
- Allocate pentesting resources.
- Rapidly mitigate vulnerabilities.
Potential Attack Visualization
Access Path Analysis
Save Wizard Bypass Login By Quickz
Where is your network at risk?
Desiderata’s network security and risk analysis feature provides detailed visibility into access controls and exposes vulnerabilities in the network. Our tools filters vulnerability scanner results, simulates potential attack paths and uses host and data values to provide clear and precise remediation steps and reduce overall exposure to access-based risk.
14
1200
+
100
%
Our Location
The very first place to turn to for informative article help is your high school or school library.